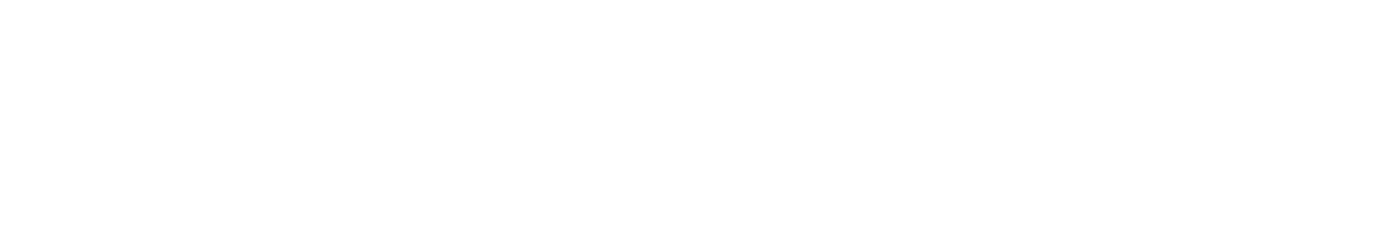
The first successful bi-directional transmission of clear speech is made by Alexander Graham Bell and his assistant Thomas Watson. Later that year, Bell made the first long distance telephone call over 16km.

Do you remember life before the internet? Do you remember using the google.com search engine for the first time? Today, PCs, smartphones and tablets dominate our lives and have become an extension of what we call a ‘normal’ life. But to understand why we think our data should be ours, we are going to take a ride into the past to see the computer in its infancy become the internet as we know it today. This story relates to every single one of us:
Punched Card Data Processing
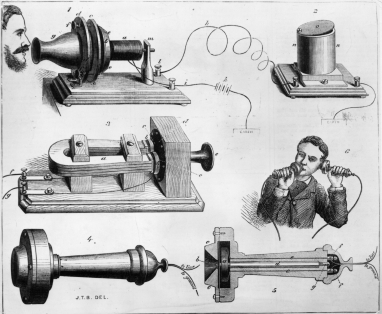
The Tabulating Machine Company specialised in the development of punch card data systems. It was intended to reduce the time and complexity needed to tabulate the 1890 Census and became the industry standard for the next 80 years of tabulating and computing data input.
A New World
The first wireless telegraphy signals are sent in the UK transmitting data between two different places by electromagnetic medium.
Radio: Communication’s Next Leap
Sound radio broadcasting was invented by Reginald Fessenden and Lee De Forest. They made the first audio radio broadcasts of entertainment and music ever made to a general audience.
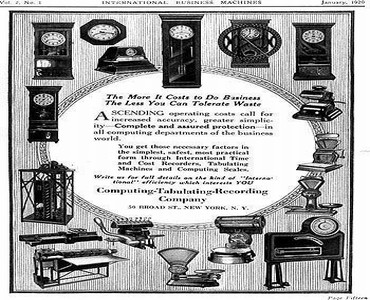
The Computing-Tabulating-Recording Company (CTR) was incorporated by a merger of the four major automated machine manufacturers, from employee time-keeping systems, to weighing scales, automatic meat slicers, and punched card equipment.
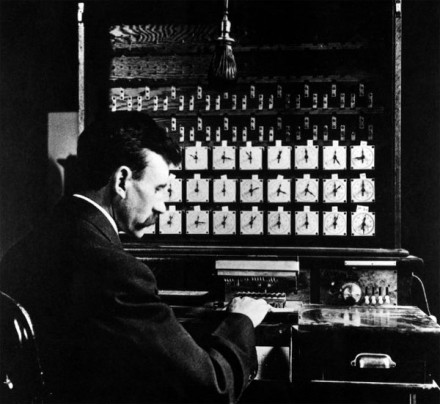
International Business Machines
CTR became the IBM that we know of today.
Brave New World
Aldous Huxley’s ‘Brave New World’ is published. It is set in London in AD 2540 and anticipates developments in reproductive technology, sleep-learning, psychological manipulation and classical conditioning. The novel expresses the widely held opinions of the era over the fear of losing individual identity in the fast-paced world of the future.
IBM & Death's Calculator
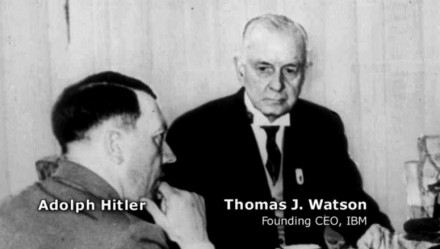
American corporation IBM and Hitler began a relationship to use a punch card system after the 1933 German census which proved pivotal to the Nazis in their efforts to identify, isolate and ultimately destroy the country’s Jewish minority. A previous estimate of 400,000 – 600,000 Jews in the nation was abandoned for a new estimate of 2 million.

The Z1 mechanical computer was designed and built by Konrad Zuse. It was the world’s first freely programmable computer in the world. It was unreliable and destroyed in the bombardment of Berlin in 1943.
The Imitation Game
The foundations of computer science are layed by Alan Turing who was responsible for code-breaking the encrypted messages of the Nazi party during WWII and instrumental in the allied victory. Turing coined the term ‘Artificial Intelligence’.
Z3 Declared "Not War Important"
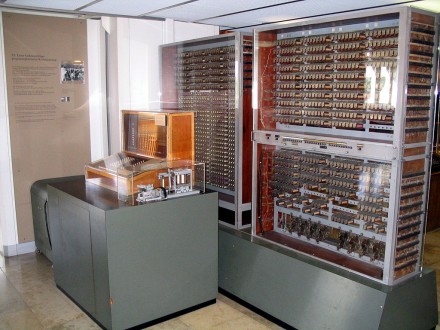
The Z3 was the world’s first working programmable, fully automatic digital computer. The German government declared it ‘not war-important’ and funding was denied. It was destroyed in 1943 during an Allied bombardment of Berlin.
Nineteen Eighty-Four
George Orwell publishes dystopian novel ‘Nineteen Eighty-Four’ set in a world of perpetual war, omnipresent government surveillance and public manipulation under the control of a privileged Inner Party elite that persecutes individualism and independent thinking as “thoughtcrimes”. The concepts of Big Brother, Thought Police and Newspeak have become common phrases in language today.
Fact: Sales of the book increased up to 7 times within the first week of the 2013 mass surveillance leaks of the NSA.
A 5mb Hard Drive

A 5 MB hard drive had to be lifted onto a plane via forklift.
The Communications Race
The USSR launches Sputnik 1, the earth’s first artificial satellite. The U.S. public reaction to the ‘Sputnik crisis’ led to the creation of the Advanced Research Projects Agency (ARPA) and increase U.S. government spending on scientific research and education.
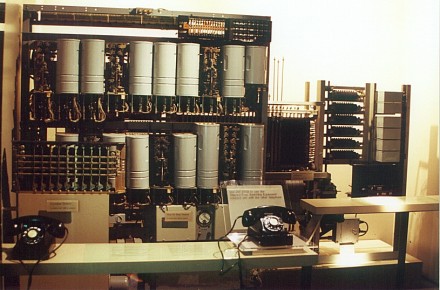
Bell Labs (USA) invents the modem, which converts digital signals to analog signals and back, enabling communication between computers.
The concept of the information network and ‘packet switching’ is established by MIT doctoral researcher Leonard Kleinrock. ARPA (Advanced Research Projects Agency) goes online in December 1969, connecting four major universities. It was specifically designed to link the country in the event that a military attack destroyed conventional communication systems.
ASCII is developed. This is the first universal standard for computers using 1’s and 0’s to represent letters allowing computers from different manufacturers to exchange data.
Communication Theory
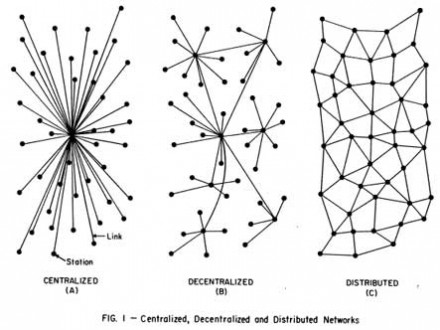
Paul Baran published his paper on ‘Distributed Communications’ that described the process which enabled data to travel faster and communications lines to be used more efficiently. It was initially designed to withstand damage from nuclear weapons.
Intel
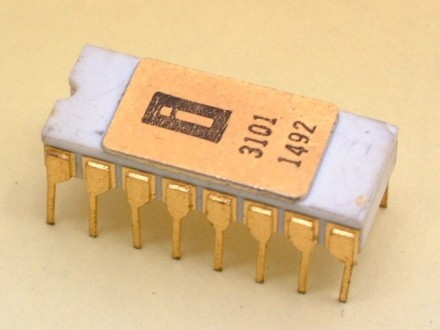
Former Fairchild engineers Gordon Moore and Robert Noyce along with Andrew Grove, a science pioneer in the semiconductor industry, founded Intel Corporation.
Intel launched its first product the 3101 Schottky TTL bipoloar 64-bit static random-access memory (SRAM).
EM@IL
Electronic mail is introduced by Ray Tomlinson. He uses the @ to distinguish between the sender’s name and network name in the email address.
Intel created the first commercially available microprocessor.
Transmission Control Protocol/Internet Protocol (TCP/IP) is designed and in 1983 it becomes the standard for communicating between computers over the internet. One of these protocols, FTP (File Transfer Protocol), allows users to log onto a remote computer, list the files, and download files from it.
Mobile Communication Becomes Reality
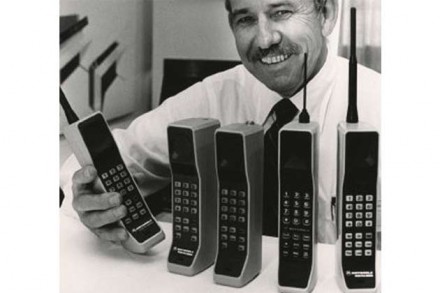
The first handheld mobile cell phone was demonstrated by Motorola.
Drones Take The Force
The U.S. military officially confirmed that they had been utilizing drones in Southeast Asia (Vietnam) to do the high-risk flying.
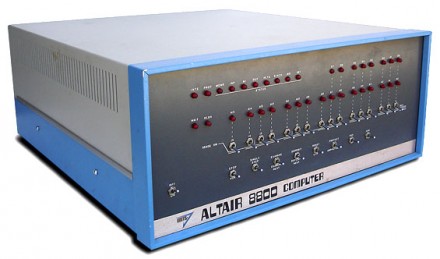
The first home computer kit is designed by Ed Roberts, the Altair 8800. It has no keyboard, mouse, monitor or software but people line the streets to purchase it.
Homebrew & Apple
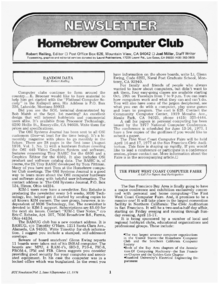
Homebrew Computer Club was formed as an early computer hobbyist group in Silicon Valley. The exchange of ideas that went on at its biweekly meetings and the club newsletter launched the personal computer revolution. It has been called, “the crucible for an entire industry”.
An Innovative Machine For Its Day
Steve Wozniak builds the first Apple Computer known as Apple I, and Steve Jobs has the idea of selling it. It was a fully assembled circuit board but users had to add a case, keyboard and monitor. This was the foundation for modern computers that can be used by anyone without any previous knowledge.
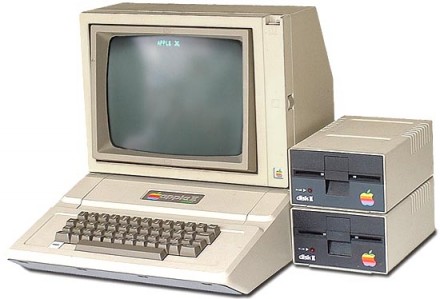
The Apple II was the first ‘appliance computer’, a completed system that could be purchased off the retail shelf, taken home, plugged in and used. The computer had colour graphics.
The Chicago Blizzard Causes The Computerized Bulletin Board System
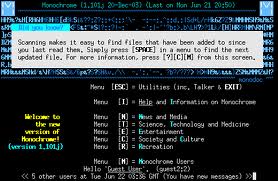
The Computerized Bulletin Board System (CBBS) officially went online. It was a public dial-up system that allowed software on the computer to pick up an incoming call, communicate with the user, and then hang up the call when the user logged off.
The first commercial automated cellular network was launched in Japan by NTT.
PC vs. Apple
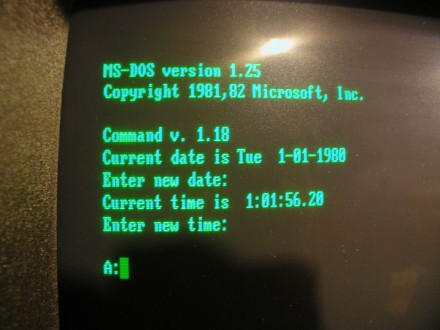
Now multi-billionaire Bill Gates developed new software for the PC and marketed its operating systems MS-DOS and Windows.

10 MB Hard Disks were available to purchase for USD$3,495. In 2005, that would have been worth $11,415.77 brand new.
The Data Law Debate
European Commission recommends guidelines governing the protection of privacy and trans-border flows of personal data. The OECD Guidelines were non-binding, and data privacy laws still vary widely across Europe.
The first experiments of reading the newspaper on a computer are made in the US. It predicted the future of receiving all newspapers and magazines by home computer.
The First of Many
Kevin Poulsen gained infamy as the first hacker by gaining unauthorized access to computers on the ARPAnet, the forerunner of the modern internet. He was seventeen at the time and instead of being charged, he went on to work as a programmer and computer security supervisor for SRI International in California.
The hackers that followed in his footsteps – Businessinsider
The Right to Privacy
The term ‘informational self-determination’ was first used in the context of a German constitutional ruling relating to personal information collected during the 1983 census. It refers to the right for an individual to decide what information about himself should be communicated to others and under what circumstances, rather than the US ‘right to privacy’ which focuses on the right to be left alone. Due to widespread resentment, the court stopped the census in 1983, and required a revision of the process.
Domain Name System (DNS) is established, with network addresses identified by extensions such as .com, .org, and .edu, rather than memorizing numerical Internet Protocol (IP) addresses (e.g. 204.62.131.129)
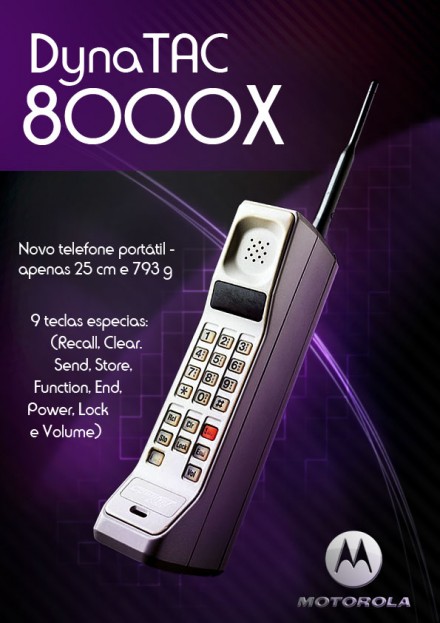
The Motofola DynaTAC 8000X was the first mobile phone to be offered commercially. It offered 30 minutes of talk time and 8 hours of standby, and an LED display for dialing. It was priced at USD$3,995.
Gibson’s Cyber-Space
William Gibson publishes his first set of novels composed of ‘Neuromancer’, ‘Count Zero’ and ‘Mona Lisa Overdrive’. They are set in a future world dominated by corporations and technology, the story focusing on the effects of technology: the unintended consequences as technology use moves from research labs onto the streets where it finds new purpose. The main theme of the trilogy is artificial intelligence.
Germany's Last Census
The modified census in West Germany was held. It was the last census to be held in Germany due to fear over abuse of the data.

A virus called The Morris Worm temporarily shuts down about 10% of the world’s internet servers. It was designed to gauge the size of the internet and it exploited vulnerabilities to gain entry to targeted systems.
Internet Commercials
CompuServe’s first internet commercial:
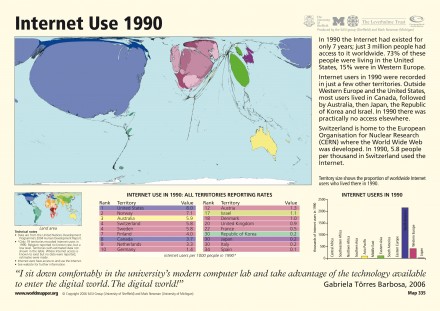
HTTP://
Tim Berners-Lee of CERN, a European research centre based in Switzerland, developed a new technique for distributing information on the internet called the World Wide Web. It is based on HTML programming (http://) which allows documents to connect to another at different sites on the internet using hyperlinks and URLs.

The Motorola MicroTAC introduced an innovative new ‘flip’ design and became the model for modern flip phones today. It was the smallest and lightest phone available at the time. It sold for between USD$2,495 and USD$3,495 and was produced into the early 1990s before being replaced by newer versions.
Intel’s Pentium Processors: A Household Name
3 Million People Worldwide Are Using The Internet
AOL
America Online (now AOL Inc.) was founded and positioned as the online service for people unfamiliar with computers. It went on to launch services with the US Department of Education as well as chat rooms, and acquired Netscape in 1999.
The first SIM card (Subscriber Identity Module) was made by Munich smart card maker Giesecke & Devrient for the Finnish wireless network operator Radiolinja. It allowed users to change phones by simply removing the SIM card from one mobile phone and inserting it into another.
CompuServe hosted the first known WYSIWYG email content and forum posts. Fonts, colours and emoticons were encoded into 7-bit text-based messages via the CompuServe Nagivator software that ran on DOS, Apple and early Windows 3.1.
The Internet in 1993
CD-ROM Replaces The Floppy Disk

Yahoo is founded by Stanford graduate students Jerry Yang and David Filo. It quickly expanded to become one of the internet’s most popular search engines.

Amazon is founded by Jeff Bezos in his garage by creating a list of 20 products which could be marketed online, finally narrowing the list to books due to the large world-wide demand for literature
The first patent for an ‘intelligent’ television system, linked with data processing systems through a digital network (or the smart TV) was filed.
The Windows Revolution

Microsoft Windows technology took off with the release of Windows 95. The anticipation of this revolutionary software created the biggest global hype in history for any single product giving the average user the capability to connect to the internet via a modem with a few simple clicks of their mouse. More games available to the computer meant people spent more time using the computer for entertainment, word processing, and surfing the internet.
32% Of Americans Own A Computer
12 million American adults are online. Internet users are not being educated about how the internet works and not aware of how much data they are revealing about themselves as they surf the web.

eBay was founded by Pierre Omidyar in 1995, and became a notable success story of the dot-com bubble; it is now a multi-billion dollar business with operations localized in over thirty countries.
ICQ was released and available for free download. Users could register an account and would be assigned a number, like a phone number, for others to be able to contact them. It was the first stand-alone instant messenger service.

The Nokia 8110 Banana phone was the first of its kind in terms of ergonomics, fitting into any pocket. The revolutionary curved design fit the natural shape of the face and its unique sliding mouthpiece allowed for maximum voice quality.
Googol?
Google is founded by Sergey Brin and Larry Page in their garage office, and they hire their first employee. By the end of the year, they are recognised in PC Magazine as the search engine of choice in the Top 100 Web Sites for 1998. The mission statement from the outset: “to organise the world’s information and make it universally accessible and useful”, and its unofficial slogan, “Don’t be evil”.
Fun Fact: The search engine was first called ‘BackRub’ but eventually they changed the name to Google originating from the word ‘googol’, the number one followed by one hundred zeros which signified that it was intended to provide large quantities of information.
Parent to PayPal, ‘Confinity’ is established as a company that develops security software for handheld devices. PayPal was then developed allowing online money transfers.
Illegal Downloading Made Easy
Peer-to-peer (P2P) file sharing becomes popular using applications such as Napster and Kazaa. This is the start of sharing music files and becomes a primary computer activity for many individuals, and opens the public up to security vulnerabilities such as viruses and hackers.
The Millennium Bug
Fear of the Millennium bug escalates leading up to New Year’s Eve. Computer and internet users are hugely concerned over their information and this shows how much computers have already become an indispensible part of our lives. However, the catastrophe never happens.
The first mobile news service delivered via SMS was launched in Finland, followed quickly by many organisations around the world providing “on-demand” and “instant” news services by SMS.
The Apple Comeback
Steve Jobs and Apple launch the iPod, a portable digital music player. This was the start of Apple brand loyalty and fanaticism that has evolved into a $182 billion empire.
544.2 Million Internet Users Worldwide
The first 3G networks started going live across the world but there were not yet available commercial handsets and thus no paying customers.
The Spam Menace
Spam becomes a server-clogging menace and accounts for about half of all emails.
MyDoom Spells Disaster
Another virus called MyDoom spreads through internet servers and about 1 in 12 email messages are infected.
The Facebook
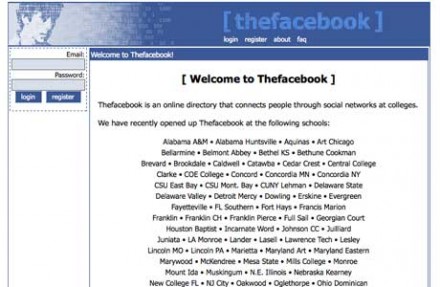
Facebook is launched by a young Mark Zuckerberg and college roommates from Harvard University. By 2006 anyone over the age of 13 can register for an account and in June 2014, there are over 1.3 billion active users.
Youtube Is Launched

Wikileaks Blows The Whistle
Wikileaks is launched to publish secret information, news leaks and classified media from anonymous sources and hacks in order to bring important news and information to the public. Releases have included documents on the Afghanistan war, corruption in Kenya and information relating to prisoners detained in the Guantanamo Bay detention camp.
23andMe, a personal genomics and biotechnology company in order to provide genetic testing and interpretation to individual consuemrs is launched by Linda Avey, PaulCusenza and Anne Wojcicki – Sergey Brin’s (of Google) wife. Uninterpreted raw genetic data is posted online and may be downloaded by customers and may include access to an assessment of inherited traits and genetic disorder risks. Since its launch it has raised huge controversial questions and the company is currently looking to move offshore.
Between 2005 and 2006, US Predator drones carried out 2,073 missions and participated in 242 separate raids.
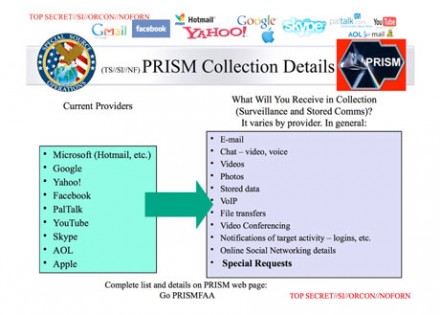
The NSA ‘PRISM’ mass electronic surveillance data mining program was launched with data provided by internet companies such as Google, Facebook, Yahoo and Microsoft.
Intel unveiled its Core microarchitecture to widespread critical acclaim, an exceptional leap in processor performance.
Apple Released The First iPhone
Europe Embraces E-commerce
Zalando is founded in Germany specialising in selling shoes, clothing and other fashion and lifestyle products online.
WhatsApp is founded by Brian Acton and Jan Koum, both former employees of Yahoo. In January 2015, it reported surpassing 700 million users.
Cryptocurrency Attracts Attention
Bitcoin is introduced as a virtual currency or ‘cryptocurrency’. Its use has attracted the attention of financial regulators, legislative bodies, law enforcement and the media listing money laundering, financing of illicit activities, theft, fraud, tax evasion and use in black markets possible with Bitcoin.
How Facebook Changed The World: The Arab Spring
The Arab Spring begins on 18 December as a revolutionary wave of demonstrations and protests, riots, and civil wars in the Arab world. As well as civil resistance techniques involving marches and rallies, social media is used to organise, communicate and raise awareness in the face of state attempts at repression and internet censorship. The result has been both positive and negative.
Mass Surveillance The World Over
TEMPORA was launched and used by the British Government Communications Headquarters (GCHQ) to buffer most internet communications to be extracted, processed and searched at a later time.
The WhatsApp Hack
A security hole in WhatsApp left user accounts open for session hijacking and packet analysis. WhatsApp communications were not encrypted.

Snapchat is founded by Evan Spiegel, Reggie Brown and Bobby Murphy, but originally launched under the name ‘Picaboo’ in Spiegel’s father’s living room.
Google Drive is launched allowing users to store documents in the cloud, share files and edit documents with collaborators.
The US Air Force Employs 7494 Drones
Pressure On Snapchat
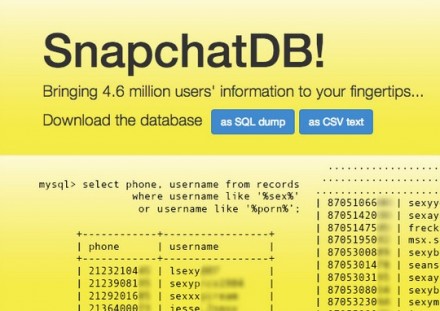
Snapchat was hacked by an anonymous group who revealed parts of approximately 4.6 million usernames and phone numbers with the objective to raise public awareness and put public pressure on Snapchat to fix the vulnerability.
Spotlight On The NSA
US Congress asked the Director of the NSA, James Clapper, if the public is tracked and what the law allows the NSA to track.
Edward Snowden - Whistleblower
Edward Snowden, NSA contractor, blew the whistle on the extent of mass data collection and characterised the governments actions as ‘dangerous’ and ‘criminal’.
Every Internet User Has A Profile
Facebook comes under fire for ‘Shadow Profiles’ and keeping the data and information that registered users choose not to show on their profile from other sources such as phone numbers and messaging. Even unregistered users have a ‘Shadow Profile’ when they have appeared in other people’s images and messages. Complaints have been filed against Facebook where this action is illegal.
Drones Are Being Used By At Least 50 Countries
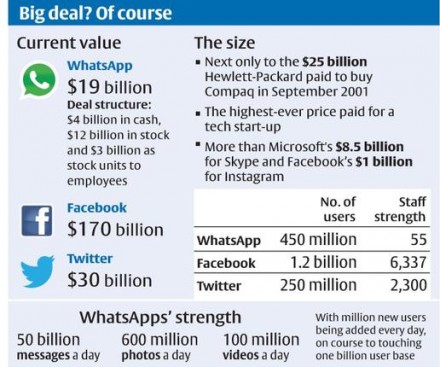
Facebook announced it was acquiring WhatsApp for US$19 billion.
The Snappening

Snapchat users were sending 700 million photos and videos per day, the company had a valuation of $10-$20 billion depending on various sources. A hacked called ‘The Snappening’ got access to 100,000 deleted Snapchat images. The Electronic Frontier Foundation (EFF) gave Snapchat the lowest rating possible for their customer privacy policy.
Apple Hack

The Apple iCloud was hacked and a collection of almost 500 private pictures of various celebrities (mostly containing nudity) were posted on the imageboard 4chan then on sites such as Tumblr and Reddit.
A Google Drive security flaw leaks sensitive and personal information stored on the cloud service.
Europe-v-Facebook

Privacy activist, Max Schrems, begins a class action suit to sue Facebook over the alleged transfer of personal data from Facebook to the US National Security Agency (NSA) as part of the NSA’s PRISM programme. His group is called ‘Europe v Facebook’.
Catastrophic Coding Error
A coding error in encryption software is discovered and transactions of usernames, passwords and personal information are stolen. Millions of banks, internet commerce companies, email services, government sites and social media sites are effected.
Spyware Virus

‘Regin’, a sophisticated malware virus used by British spy agency GCHQ was discovered by German publications. It was stealthy and enabled customised spying and long-term mass surveillance operations against targets. German newspaper Bild reported that Regin was found on a USB flash drive used by a staff member of Chancellor Angela Merkel.
Hollywood Relives 1980s Silicon Valley
TV Series ‘Silicon Valley’ airs in the US. It was inspired by Mike Judge’s experience as an engineer in Silicon Valley in the 1980s.
There Are More Than 7 Billion Mobile Phone Subscribers Worldwide
Tech Giant Fiscal Year 2014 Revenues
Google: $66 billion
Facebook: $12.47 billion
Microsoft: $5.5 billion
Yahoo: $4.61 billion
AOL: $2.52 billion
Twitter: $1.4 billion
What Happened To Privacy?
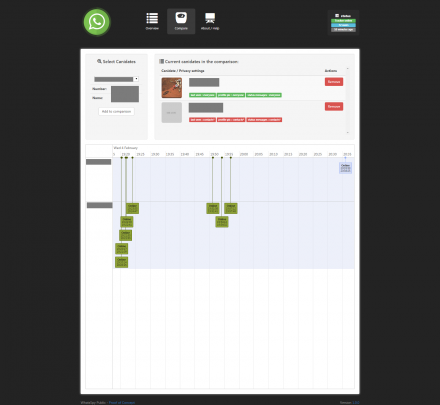
Privacy settings on WhatsApp can be easily bypassed by simple software called “WhatsSpy Public”.

Facebook changes its privacy policy again allowing government intelligence operations easier access to user data.
Who Is Listening?
Smart TVs are expected to become the dominant form of television. However, it has been discovered that the TV has the capability to eavesdrop on conversations and target ads to the user causing privacy concerns specifically around the Samsung Smart TV.
#Occupy
Occupy Wall Street is the name given to a protest movement that began on September 17 In Zuccotti Park, NYC. It receives global attention and spawned the Occupy movement against social and economic inequality worldwide. The main issues raised are social and economic inequality, greed, corruption and the perceived undue influence of corporations on government.
#EuroMaiden
Ukraine demonstrations turn violent and Markiyan Matsekh communicates the message of peaceful protest by playing classical music from a piano in front of police lines. The piano is painted in the colours of the Ukrainian flag and the European Union and becomes a sensation on social media and youtube.
A Tool For Freedom And Terror
The internet becomes an instrument of terror as well as liberation. Images and videos from battle fronts are spread through social media to frighten and demoralise enemies resulting in a new digital propaganda war.
– today –
Who owns your data?
We have been groomed into a society that willingly gives up their data for the use of ‘free’ services and to be a part of brand loyalty. But we are also now realising the dangerous position that this good faith and naivety has put us in. With the explosion of technological innovation bringing the laptop, tablet and smartphone, it has never been so easy for large corporations and governments to obtain access to our personal data for their own use and profit.
Even if sites like WikiLeaks or groups such as Anonymous can continue to expose government misdealings, they are only representing a drop in the ocean when it comes to what is being done with our data. Google, Facebook, Yahoo, Apple and other similar services provide such attractive products we are so easily swept into allowing them to determine our information, preferenes and interests. It’s time to ask whether this blind hand out of our data should be allowed to determine our future.
– The Future –
Democracy or monopoly?
If we choose to continue down the path of ultimate trust in Google, Facebook, Apple and Microsoft or any other company with our data, our information will only become more and more publicly available and spied on. Unless we put a stop to it, they will never be able to satiate their appetite for our user profiles. Which future do you choose?
Free Your Data is committed to enacting a law that states: “Any company with more than 1 million users is required to provide any active or inactive user’s data to them free of charge, immediately and in a machine-readable form.”
Our data reflects our power to live as individuals in a democratic society representing who we are in the digital world. There is potential for new industry and new business models to develop that appreciate the value of data and are willing to work ethically with the data of individuals.
2015 – 2020: Smart Grid.
Under the paper-thin veil of “modernising” the energy and utility industries, surveillance devices called Smart Meters are deployed into people’s homes which provide a perpetual news feed to Big Energy and their government data brokers (in the UK, it’s called the DCC) about how household occupants are consuming energy and behaving. This data can be passed on to other 3rd parties such as insurers, pharmaceutical companies, marketers and law enforcement for further data mining and analysis.
Numerous publicly available documents show that these meters — especially when combined with new “Internet of Things” RFID-enabled devices, appliances and products — are capable of recording very sensitive information about people’s lives at home, ranging from what they eat and when they sleep to whether they have mental health issues. Data analytics companies have shown the patterns of behaviour can be used to predict occurences within a home too, as well as occupants state of well-being.
Interestingly, IBM — who created Hollerith — are a very significant player in the Internet of Things and Smart Grid — technologies which will provide a means to constantly gather data on all members of the population.
Get good GRADES and do not let your lecturers frustrate your future. The other advantage is that no one ever gets to find out. This Guru makes the security of his clients is first priority…He is specialized in UNIVERSITY/COLLEGE GRADE CHANGE/UPGRADE contact, STUDENT TRANSFER TRANSCRIPT CHANGE?..His service is fast and secured. He does SCHOOL GRADE, TRANSCRIPT CHANGE AND TRANSFER for students all over the world (ASIA, NORTH AMERICA, SOUTH AMERICA, AFRICA, ASIA, EUROPE and Australia). No matter your location. If you have problem with your SCHOOL GRADES If you graduated and did not have the right GRADEs If you want to UPGRADE your TRANSCRIPT and get your desired certificate If you want to transfer to another school?..Contact Matrix “ (704) 471-6204″ or Matrixhackka007@gmail.com…… He’s a different class he helped me and a few of my school colleagues.